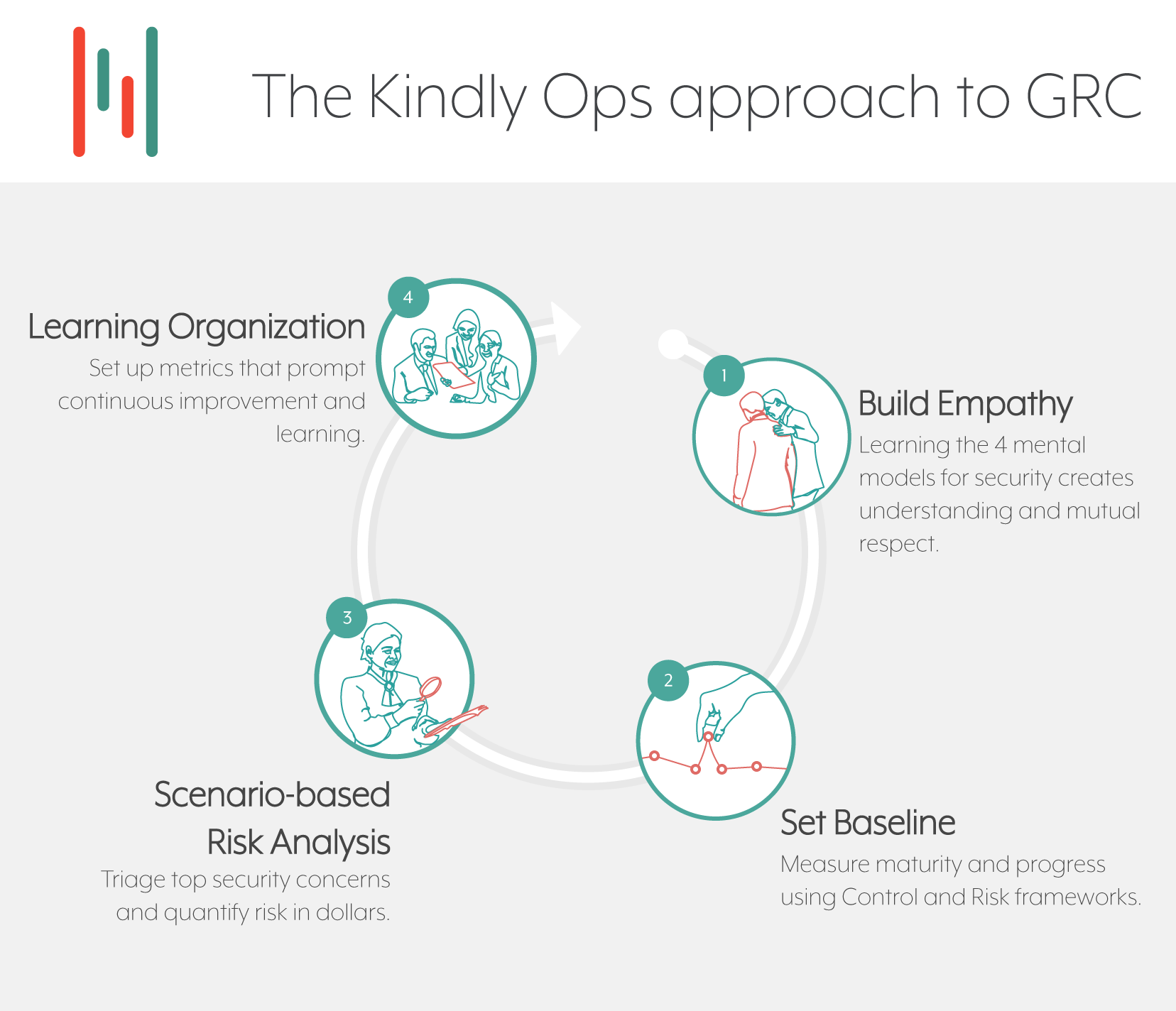
Start with Empathy
First, we start with empathy. Helping the team to become aware of different mental models around safety and risk doesn’t take long, and it makes a big difference in their ability to cooperate and support other phases of the work. We like to start with the Security Culture Diagnostic Survey, published under a Creative Commons license by Dr. Lance Hayden.
Set a baseline
While it’s common to want to start by doing risk analysis, we recommend getting started with a prescriptive controls framework. If you haven’t already selected one, the NIST Cybersecurity Framework (CSF) and/or the CIS Critical Security Controls are good minimal starting points. Because these frameworks prescribe common good practices based on observed effectiveness across a wide variety of companies and have mappings into more detailed frameworks, work done implementing these will be useful no matter what you turn up in your risk analysis.
This work also helps your team figure out how to follow standards and show evidence of compliance. Later as you customize the controls for your organization, implenting revised standards will be easier.
Do some risk analysis
The most challenging part of the cycle, conducting risk analysis is where cyber security has a history of sloppy analysis. Quantitative risk techniques such as FAIR are gaining popularity and provide useful structure to risk analysis and makes it more useful for informing business decisions.
Start the learning cycle
One weakness with the baseline or maturity model approach is that while organizations experience a big improvement as they initially adopt a model and reach maturity, once they reach the target level improvement tends to stop.
Setting specific metrics around learning will drive continuous improvement year after year, and prevent rules from becoming detached from the risks that the rules were originally intended to mitigate.
The model